Re-taking SC-300 in 2 Days (One-liner Notes)
I am re-taking SC-300 in 2 days - still a bit nervous. Here are the one-liner notes from ChatGPT. I feel like I am not ready yet. But we'll see. Good lucks to me!
Microsoft 365 groups can only contain users.
Security groups can contain users, devices, and other groups.
Only security groups can be used for group-based licensing.
Microsoft 365 groups cannot be used for license assignment.
Dynamic device groups cannot be used for user licensing.
Administrative Unit (AU) scope does not apply through group membership.
AU-scoped admins can manage only direct members of the AU.
User Access Administrator manages Azure RBAC role assignments.
Privileged Role Administrator manages Entra ID role assignments.
Global Administrator is not the least-privileged answer in exams.
Entra ID roles ≠ Azure RBAC roles (directory vs resource scope).
User-assigned managed identities can be used across regions.
Managed identities require resource support, not same region.
Password Hash Sync allows cloud authentication independent of ADFS.
Without writeback, cloud changes do not sync back to on-prem.
In hybrid, on-prem is source of authority for synced users.
Duplicate proxyAddresses cause AttributeValueMustBeUnique errors.
New object conflicting during sync causes InvalidSoftMatch errors.
proxyAddresses must be globally unique across tenant.
SMTP (uppercase) = primary email, smtp (lowercase) = alias.
B2B guest users authenticate with their original identity provider.
To allow external users, create a guest user (B2B).
External collaboration settings do not grant access by themselves.
Federation (WS-Fed/SAML) is for org-to-org trust, not individual users.
Microsoft accounts (Outlook/Hotmail) are supported natively in B2B.
Nested groups are allowed in security groups only.
Microsoft 365 groups do not support nested groups.
Dynamic user groups evaluate user attributes only.
Dynamic device groups evaluate device attributes only.
License assignment requires user objects, not devices.
Cloud-only groups can include synced users.
Synced users should be managed on-prem for consistency.
PIM provides just-in-time role activation.
Eligible roles in PIM require activation before use.
Conditional Access policies evaluate after authentication.
Authentication = identity verification; Authorization = access decision.
MFA is enforced via Conditional Access or Security Defaults.
Security Defaults apply baseline protections tenant-wide.
Break-glass accounts should be excluded from Conditional Access.
Microsoft 365 groups can only contain users (no groups, no devices).
Security groups can contain users, devices, and other security groups (nesting allowed).
Microsoft 365 groups cannot be nested into any group.
Dynamic groups cannot be used for role-assignable groups.
Role-assignable groups must be Assigned membership and set at creation time.
Role-assignable flag cannot be enabled after a group is created.
Group-based licensing applies only to direct user members, not nested groups.
Dynamic device groups cannot be used for user license assignment.
Azure RBAC roles can be assigned to users, groups, service principals, and managed identities.
A VM with a system-assigned identity is a valid RBAC principal.
Enterprise applications are service principals and can receive RBAC roles.
Conditional Access client apps condition controls browser vs mobile vs desktop vs legacy auth.
Conditional Access session controls apply only to browser sessions.
Blocking downloads/sync clients requires client apps condition, not just session control.
“Minimize administrative effort” → prefer built-in roles over custom roles.
“Strict least privilege” → consider custom roles if built-in roles are too broad.
Helpdesk Administrator role includes service requests, service health, and support tickets.
Custom roles require more effort and are rarely correct if a built-in role fits.
Security Reader = read-only access to security/governance data.
Security Operator = limited operational actions but mostly read-only.
Security Administrator = can configure security features.
Conditional Access Administrator manages CA policies but not Identity Protection policies.
User risk policy can enforce password reset for compromised users.
Sign-in risk policy controls access (MFA/block), not password reset.
SSPR for synced users requires password writeback enabled.
Pass-through Authentication (PTA) authenticates users against on-prem AD.
OU filtering in Azure AD Connect controls which users are synced to Entra ID.
Users not synced to Entra ID cannot access SharePoint Online.
Device limit per user is configured in Device settings.
Managed identities remove the need for storing credentials in apps.
System-assigned managed identity is tied to one resource only.
User-assigned managed identity can be shared across multiple resources.
“Only this resource” → use system-assigned managed identity.
Access Reviews with “Users review their own access” = only the user can review themselves.
Guest users can perform self-access reviews if configured.
Identity Secure Score updates require Security Administrator or higher.
Security Operator cannot update Secure Score (read-only).
Role comparison tasks are fastest in Microsoft 365 admin center.
Deep RBAC analysis is done in Microsoft Entra admin center.
PIM enables just-in-time role activation but does not grant permissions by itself.
Administrative Units scope role permissions but do not grant permissions.
Azure AD Password Protection prevents weak passwords, not account compromise.
Marking a user as compromised raises risk level to trigger user risk policy.
Steem to the Moon🚀!
- You can rent Steem Power via rentsp!
- You can swap the TRON:TRX/USDT/USDD to STEEM via tron2steem!
- You can swap the STEEM/SBD to SUI via steem2sui!
- You can swap the STEEM/SBD to SOL Solana via steem2sol!
- You can swap the STEEM/SBD to ETH Ethereum via steem2eth!
- You can swap the STEEM/SBD to Tether USDT (TRC-20) via steem2usdt!
- You can swap the STEEM/SBD to TRX (TRON) via steem2trx!
- You can swap the STEEM/SBD to BTS (BitShares) via steem2bts!
- Register a free STEEM account at SteemYY!
- Steem Block Explorer
- ChatGPT/Steem Integration: You can type !ask command to invoke ChatGPT
- Steem Witness Table and API
- Other Steem Tools
Support me, thank you!
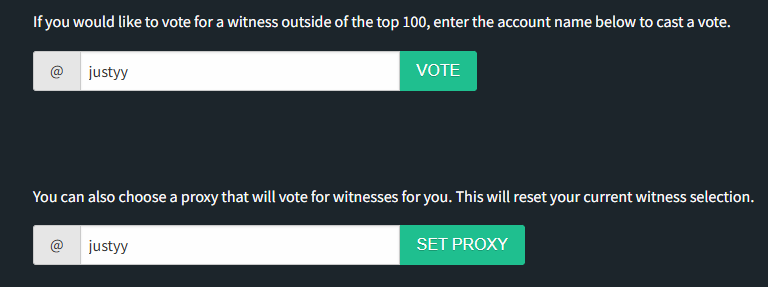
Why you should vote me? My contributions
Please vote me as a witness or set me as a proxy via https://steemitwallet.com/~witnesses