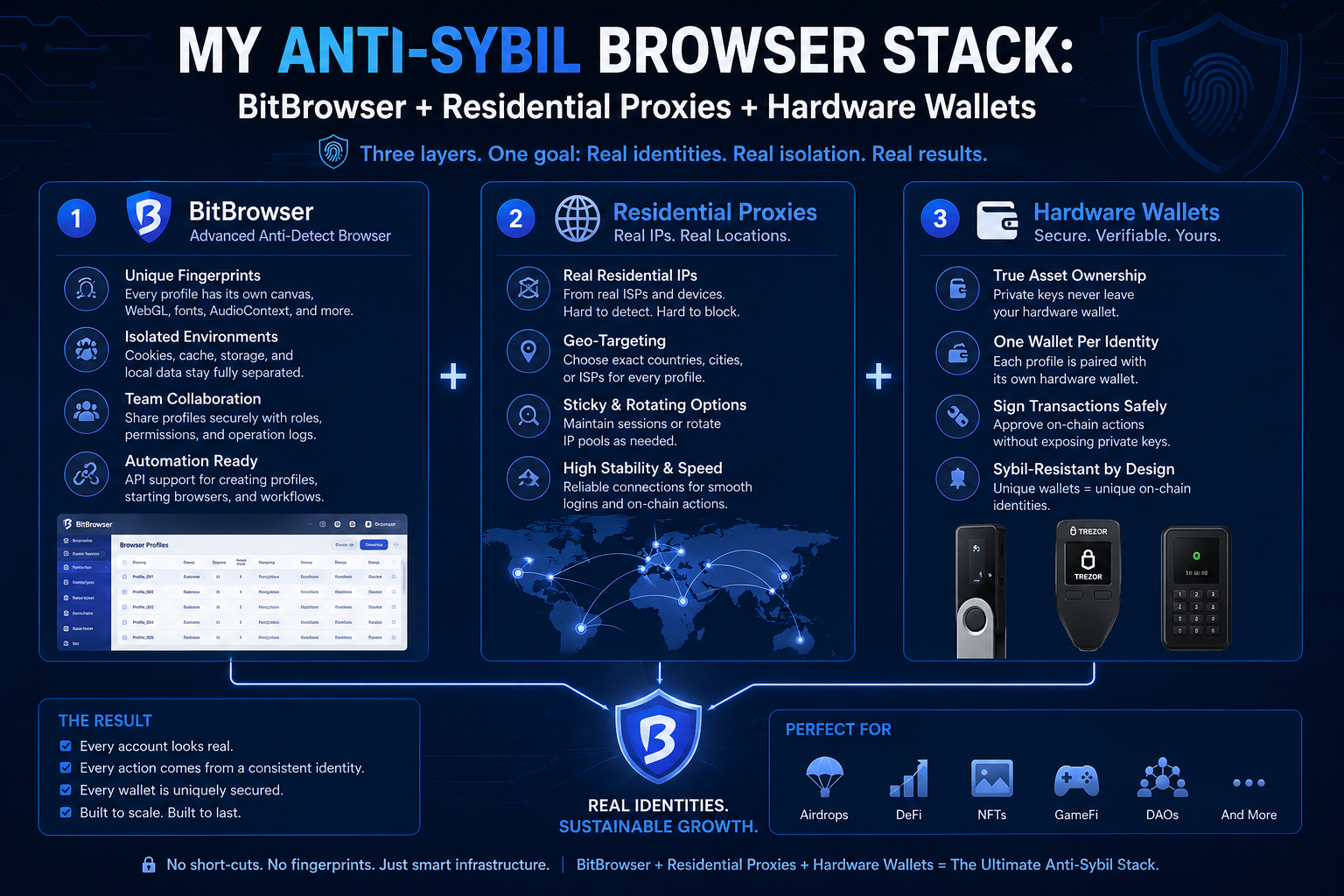
My Anti-Sybil Browser Stack: BitBrowser + Residential Proxies + Hardware Wallets
After two years of participating in crypto ecosystems across multiple wallets, I have learned one thing the hard way: the biggest threat to your airdrop eligibility and on-chain privacy is not the blockchain itself — it is your browser. The chain is pseudonymous by design. But the off-chain layer, the browser sessions you use to interact with dApps, testnets, and protocol frontends, leaks far more information than most people realize.
This post covers the exact stack I use to keep my wallets operationally independent from each other, protect my on-chain privacy across chains, and maintain clean separation between wallet identities when interacting with protocol frontends.
Why Browser-Level Separation Matters for Crypto
Most people in the crypto space focus heavily on wallet hygiene — never reusing addresses, using hardware wallets, keeping funds separated across chains. All of that is correct. But then they access multiple wallet frontends from the same browser session, and that is where the separation breaks down.
Here is what happens when you connect Wallet A and Wallet B to any dApp frontend from the same browser:
The frontend logs your browser fingerprint alongside the wallet address. Browser fingerprints are composed of your screen resolution, graphics card data, installed fonts, Canvas rendering output, WebGL renderer, timezone, and dozens of other parameters. If two wallet connections share the same fingerprint — even if the wallet addresses are completely different and funded from different sources — the frontend has a strong signal that those wallets belong to the same person.
Projects doing Sybil analysis before token distributions use exactly this kind of data. They correlate on-chain activity with off-chain signals collected at the frontend level, including browser fingerprints, IP addresses, and session timing. Wallets that share any of these signals get clustered together and treated as a single entity for eligibility purposes.
This is why wallet hygiene alone is not enough. You need browser hygiene to match it.
Layer 1: BitBrowser for Wallet Profile Isolation
The foundation of my stack is BitBrowser, an antidetect browser that creates fully isolated browser profiles with unique and persistent fingerprints.
The setup is straightforward: each wallet gets its own dedicated browser profile. When I open Profile 1 for Wallet A, it presents a specific Canvas fingerprint, WebGL renderer, screen resolution, fonts, and User Agent that are unique to that profile. Profile 2 for Wallet B presents a completely different set of parameters. From the perspective of any dApp frontend or analytics layer, these look like two different devices operated by two different users.
What makes this work for crypto specifically is the persistence of profiles. The fingerprint does not randomize on every session — it stays consistent. This matters because some protocol frontends track returning users and flag wallets that appear with a different device signature on each visit. Consistency looks like a real user. Random fingerprints on every session look like automated tooling.
BitBrowser also provides complete isolation of cookies, localStorage, and IndexedDB between profiles. This is important when interacting with dApp frontends because many of them store wallet connection state, session tokens, and user preferences in localStorage. If that data leaks between profiles, it creates a linkage signal even when the fingerprints themselves are clean.
I currently manage 18 wallets across several ecosystems this way. Each one has its own BitBrowser profile, its own proxy, and its own hardware wallet derivation path. No profile has ever been open at the same time as another during a wallet connection — I work through them sequentially to avoid any risk of simultaneous session correlation.
Layer 2: Residential Proxies for IP Isolation
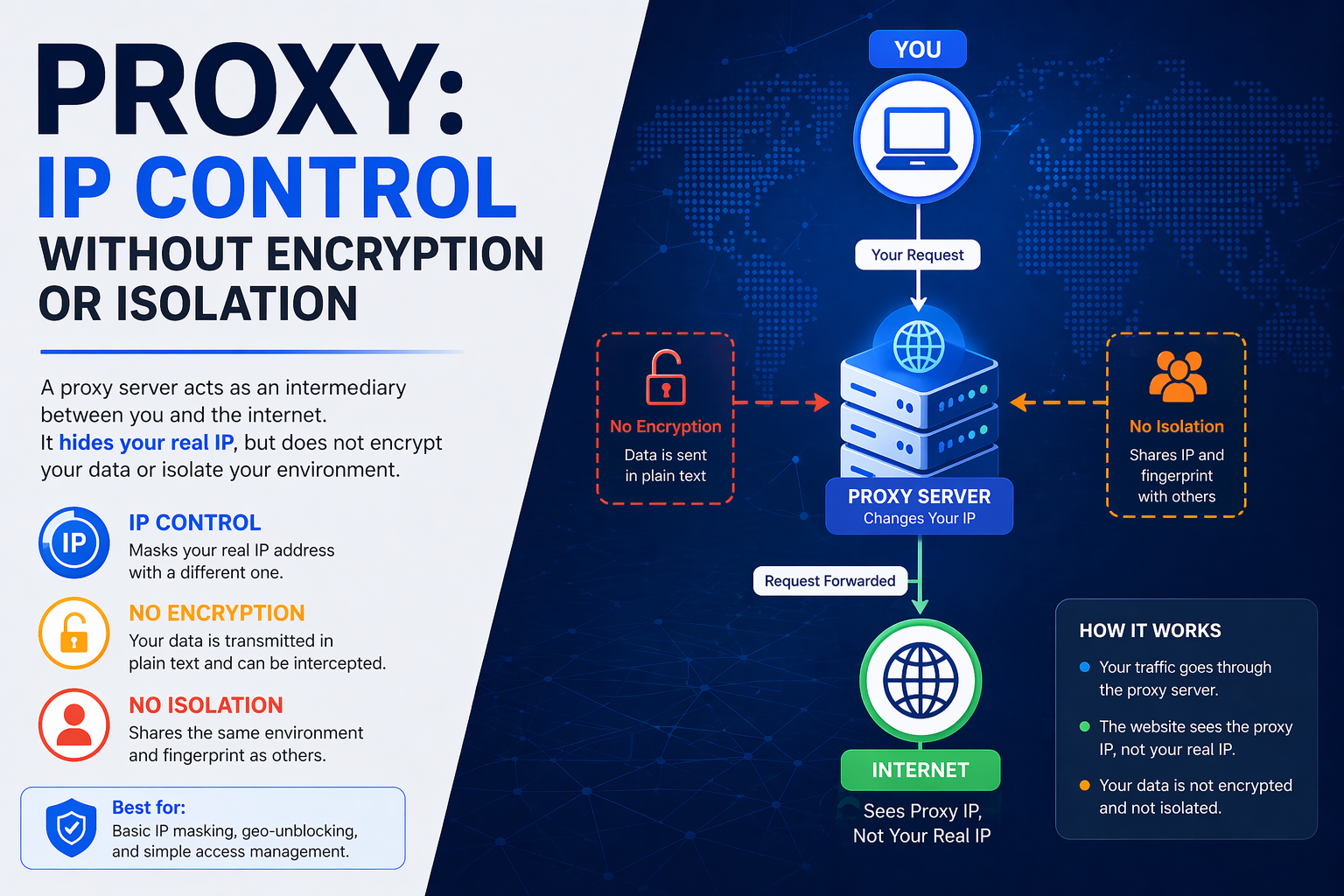
Browser fingerprint isolation handles the device identity layer. IP isolation handles the network layer. Both are necessary.
Each BitBrowser profile has a dedicated residential proxy assigned directly in the profile settings. Residential proxies use IP addresses allocated by real ISPs to real home users, which means they blend naturally into organic traffic. Datacenter proxies are flagged by most protocol frontends and analytics tools because their IP ranges are well-documented and widely blacklisted.
The rules I follow for proxy assignment:
One IP per wallet profile, no sharing. If two wallet profiles ever share an IP address, even briefly, that creates a network-level correlation that can survive fingerprint separation.
Sticky sessions. The proxy IP should not rotate during a session. A wallet connection that switches IP mid-interaction looks like network anomaly activity.
Geo-consistency. I keep the same geographic location for each profile across sessions. A wallet that connects from New York one week and Singapore the next raises flags in behavioral analysis.
The proxy is assigned inside BitBrowser's profile configuration, so it loads automatically every time I open that profile. There is no risk of accidentally opening a wallet session with the wrong IP or no proxy at all.
Layer 3: Hardware Wallets for On-Chain Security
The first two layers protect my off-chain identity. Hardware wallets protect my on-chain assets and signing operations.
I use hardware wallets with multiple derivation paths, which allows me to maintain distinct wallet addresses under separate HD paths without needing multiple physical devices. Each wallet profile in BitBrowser corresponds to a specific derivation path — so even if the browser profile is isolated and the IP is clean, the signing always happens on hardware, keeping private keys completely off the machine.
For wallets holding any meaningful value, hardware signing is non-negotiable. Browser-based hot wallets are exposed to JavaScript injection through dApp frontends, compromised browser extensions, and clipboard hijacking. Hardware wallets eliminate all of these attack vectors by keeping the signing operation air-gapped from the browser environment.
The interaction model for each wallet session looks like this: open the dedicated BitBrowser profile, connect the hardware wallet to the browser via its web interface, interact with the dApp frontend, confirm transactions on the hardware device, close the profile. Clean, contained, repeatable.
Mobile Sessions: BitCloudPhone
Some protocols and ecosystems have mobile-native frontends, mobile-specific task tracking, or social components that are better accessed through apps than desktop browsers. For these I use BitCloudPhone, which provides isolated cloud Android environments with independent device identities.
Each cloud phone has its own IMEI, device fingerprint, and network parameters. I assign one cloud phone per wallet that requires mobile interaction — for example, protocols with Telegram-based task verification or mobile app engagement requirements. The cloud phone operates entirely independently from the desktop BitBrowser profile, so the two channels do not create a cross-device correlation signal.
This matters because some Sybil detection models specifically look for wallets that only interact through desktop and never through mobile, or vice versa. Having both channels covered — and kept properly separated — makes each wallet profile behaviorally more complete.
Operational Practices That Matter as Much as the Tools
The technical stack covers the fingerprint and network layers, but operational discipline covers the behavioral layer. Here is what I do consistently:
Stagger interaction timing. I do not interact with the same protocol frontend from multiple wallet profiles in the same time window. Session timing clustering is a Sybil signal — if ten wallet addresses all interact with a testnet within the same 20-minute window from the same general network region, that pattern stands out.
Vary interaction depth per wallet. Real users interact differently. Some explore more features, some just do core transactions, some come back repeatedly over days. I vary the depth and frequency of interactions across profiles to produce more organic behavioral patterns rather than identical sequences.
Never cross-contaminate. I never copy a wallet address from one profile and paste it into another profile's browser session. I never send funds directly between wallets that are managed in the same operational stack without routing through an intermediary. On-chain transaction graph analysis is a separate but related layer of Sybil detection that requires its own hygiene practices.
Keep profiles stable. I do not change the fingerprint parameters of an existing profile, ever. If a profile needs to be retired, I retire it and create a new one from scratch. Changing fingerprint parameters on an active profile creates a historical anomaly in frontend session logs.
The Full Stack at a Glance
| Component | Tool | Purpose |
|---|---|---|
| Browser profile isolation | BitBrowser | Unique fingerprint per wallet |
| IP isolation | Residential proxies (1 per profile) | Independent network identity |
| Asset security | Hardware wallet (multiple derivation paths) | Air-gapped signing |
| Mobile isolation | BitCloudPhone | Independent mobile identity per wallet |
| Behavioral layer | Operational discipline | Organic interaction patterns |
Final Thoughts
Sybil detection has become significantly more sophisticated over the last two years. Projects are no longer just checking for shared on-chain transaction origins — they are correlating frontend session data, browser fingerprints, IP clustering, interaction timing, and behavioral patterns. Wallets that look identical off-chain get treated as identical regardless of on-chain separation.
The stack I have described here addresses each of those detection vectors independently. BitBrowser handles fingerprint and session isolation. Residential proxies handle IP isolation. Hardware wallets handle key security. BitCloudPhone handles mobile identity separation. Operational discipline handles behavioral patterns.
If you are serious about maintaining independent wallet identities across ecosystems, the starting point is setting up BitBrowser and building one clean profile per wallet from day one. Retrofitting isolation onto an already-active stack is significantly harder than building it correctly from the start.
Stay clean on-chain and off-chain.