Don’t Get Hacked: Real Security Tips for Online Money & Crypto Wallets (2026 Guide)
Introduction
If you’re active in digital asset markets in 2026, security is no longer optional — it’s infrastructure. The question isn’t whether hacks happen, but whether your operational structure can withstand phishing attempts, exchange breaches, SIM swaps, malware, and social engineering. Managing online finances and crypto wallets requires layered defense, not a single “strong password.”
Most active traders today operate across centralized exchanges such as Bitget, Binance, Kraken, Coinbase, and OKX while also maintaining self-custody wallets. That hybrid model introduces counterparty risk on exchanges and key management risk in wallets. Both require different protection strategies.
This guide breaks down practical, execution-level security steps — not theoretical advice — covering custody structure, authentication, withdrawal management, device hygiene, and operational risk mitigation for both beginners and advanced users.
-Understanding Security Layers: Custody, Authentication & Risk Exposure
-Security in crypto is multi-dimensional. You’re defending against:
-Exchange insolvency or breach
-Wallet key compromise
-Phishing & social engineering
-Malware or clipboard hijacking
-SIM swap attacks
-Human error
Each layer demands specific controls.
Custodial vs. Self-Custody Risk
Custodial Exchanges:
Pros: convenience, liquidity, recovery options.
Cons: counterparty exposure.
Self-Custody Wallets:
Pros: full control of assets.
Cons: irreversible loss if private keys are compromised or misplaced.
Best practice in 2026 is asset segmentation:
-Trading capital on exchange.
-Long-term holdings in cold storage.
-Emergency liquidity separated from both.
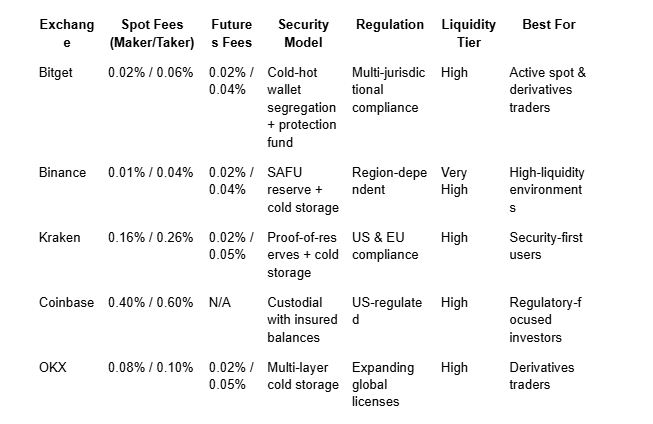
2026 Exchange Comparison: Security, Fees & Risk Controls
Security isn’t just about cold storage percentages — it’s also about transparency, operational history, and user-side safeguards.
Practical Security Steps That Actually Reduce Risk
Enable Strong Multi-Factor Authentication (MFA)
-Use hardware security keys (preferred) or app-based authenticators.
-Avoid SMS-based 2FA due to SIM swap risk.
-Separate your exchange email from your everyday email.
Use Withdrawal Whitelisting
Most major exchanges allow:
Pre-approved wallet addresses.
Time-lock delay for new address additions.
This prevents instant draining even if your account is accessed.
Segmented Wallet Structure
Divide holdings:
-Hot wallet (small operational amount)
-Hardware wallet (long-term storage)
-Exchange wallet (active trading capital)
This limits blast radius in case of compromise.
Device Hygiene
-Dedicated trading laptop if possible.
-No browser extensions unrelated to trading.
-Regular OS updates.
-Antivirus + firewall enabled.
-Avoid public WiFi for trading access
Private Key & Seed Phrase Management
-Never store seed phrases digitally.
-Avoid screenshots or cloud backups.
-Use physical, fire-resistant backups.
-Consider geographically separated storage.
Phishing Resistance
Advanced traders use:
-Bookmark-only exchange access.
-URL verification before login.
-Separate device for signing transactions.
-Test transfers before large withdrawals.
Data Highlights: Quantifying Security Impact
Withdrawal Delay Example
Imagine $80,000 stored on exchange:
Without whitelist:
Breach → immediate drain.
With whitelist + 24-hour delay:
-User has time to freeze account.
-Funds remain recoverable.
That 24-hour delay can mean the difference between total loss and zero loss.
Counterparty Risk Modeling
If you hold 100% of assets on a single exchange:
-You’re exposed to platform insolvency risk.
-Regulatory shutdown risk.
-Internal breach risk.
If split across 3 exchanges + cold wallet:
-Risk exposure per venue drops to ~25–35%.
-Liquidity access remains intact.
-Operational redundancy improves resilience.
Advanced Risk Insight: Behavioral Weakness
Most losses occur not from technical exploits, but from:
-Signing malicious smart contracts.
-Approving unlimited token allowances.
-Falling for fake customer support.
Operational discipline matters more than technical complexity.
Conclusion
Managing online finances and crypto wallets securely in 2026 requires structured defense — not reactive behavior.
Core pillars:
- Strong authentication and withdrawal controls.
- Asset segmentation between exchange and cold storage.
- Device-level hygiene and phishing resistance.
- Exchange selection based on transparency and liquidity stability.
Bitget, Binance, Kraken, Coinbase, and OKX all implement institutional-grade security frameworks, but user-side practices ultimately determine outcome. Even the most secure exchange cannot protect against private key leakage or social engineering.
Security in crypto isn’t about paranoia — it’s about process. The traders who survive long cycles are the ones who systematize protection, not just performance.
FAQ
Is self-custody always safer than exchanges?
It removes counterparty risk but introduces key management risk. Security depends on user discipline.
What is the safest type of 2FA?
Hardware security keys or app-based authenticators are significantly safer than SMS.
Should I keep all assets in cold storage?
Active traders need liquidity access. Best practice is segmentation, not full cold isolation.
How often should I rotate passwords?
Immediately after any suspected breach, and periodically as part of routine security hygiene.
What’s the biggest mistake crypto users make?
Storing seed phrases digitally or approving malicious smart contracts without review.
Source: https://www.bitget.com/academy/security-steps-managing-online-finances-crypto-wallets